| THE IT SECURITY PROFESSIONAL |
Barlowtek
The It security Pro
Helping Organizations Understand IT Security
&
Best Practices
The Rogue EmployeeWe have all met those technical people that have worked for our companies that have kept to themselves and may have had some sort of run in with management, and now they want to get back at the company. How do we as IT Security Professionals protect against this threat? How do we identify if one of our own turns rogue? Security ControlsWhile most of us implement security controls for the protection of the company or business as a whole, we have to keep in mind that there are those that will try to circumvent those controls. Here are the top areas that you should be looking at to tell if an employee has gone rogue:
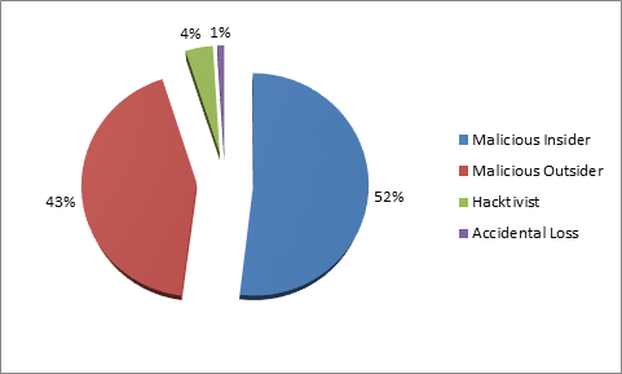
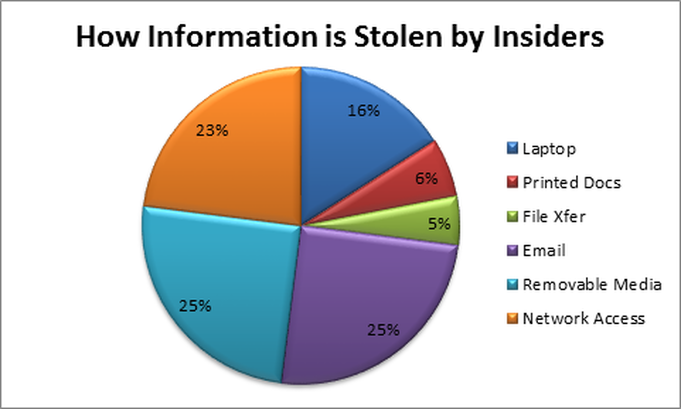
Motivations Motivation may be hard to determine for a potential insider threat. With so many variables, it may be hard to tell if it is one or multiples of reasons for it to happen. Employees that know the systems like Administrators may be the core focus of your efforts for monitoring. Nevertheless, the average user may also have motivations in which they want to capitalize on. If a user has a particular ax to grind against the business, then they may need to be watched more than others due to their proclivity towards having ill will towards the company. This should be an area that is discussed with the HR Manager or others to determine the type of impact that may happen if it is suspected. With that in mind, taking action against a potential threat may be more prudent than waiting to see if something else happens. Out for Themselves When being an IT Security Professional, it is important that you are a student of human behavior and that you understand human motivations. Whether it is designing a monitoring program or teaching new users the ins and outs of social media security. You will be called upon to determine if someone is a possible threat to your organization. However, how do you know it isn’t something about the user taking work home with them? While the motives of those that will undermine a company or business that they work for may be varied. It is important to keep in mind; our job is to protect the company we work for. Looking for the signs and behaviors of our fellow co-workers may be one of the hardest aspects of our job. Helping someone out is one thing, but helping them exfilarate data out of the business is another. Monitoring Internal Threats While we have a need to monitor our networks and those that use them. We also have to protect our businesses from all threats that may take advantage of possible cracks in our controls. The internal threat is the most impactful and the most significant threat that we face today. Countless times over the last few years we have seen rogue user exfiltration of controlled data or information. While most would agree that there is never a good reason to have organizational data leaked to the public. It is important to remember that these rogue users are usually breaking the law by transferring this information out of the business, or are breaking the security policies that they said that they would uphold when they were hired. Monitoring everyone on the network and scrutinizing every action or inaction would tie up resources. Automated Monitoring Automation has enabled the IT Security Professional to be able to monitor the network and follow up with suspicious incidents when they occur. This can be accomplished with the use of a Data Loss Protection (DLP) solution that monitors the content of information that moves across or out of the network. The key to this solution is that it is actively monitored and that incidents are followed up and addressed when they happen. While behavior may be a dead giveaway, it may be difficult to detect by managers or supervisors if they have not encountered a similar situation in the past. This is where the automated monitoring of data moving across the network will be helpful. This will provide a trail that the network admins can look at and determine if the information that is leaving the network has been authorized or if it is out of character for the user. Potential Loss
When it comes to an internal threat, the most impact that they will have will be on the loss of proprietary intellectual property (IP) that they had access to. The loss of this data may potentially affect the company in ways that can’t be directly determined, but if your company is developing a product or service that others are not, then you have a need to control this data. If the business loses the IP they have been working on, the business may end up losing out to a competitor. Just like any other risk that a company may encounter, the loss of data will have a cost associated with it. Whether it is the loss of the work done by the employee, which they took with them, or the IP that they employee helped developed. The company has already invested that money in the product or services that the employee had a help in producing. The loss here is due to the impact that it may have on the future of the company. Loss may be hard to calculate, but the impact could be devastating, especially to a small business or start-up. Summary While we take a look at the whole picture when assessing the security posture of our companies. Sometimes the hardest to see is what is in the mirror. Insider attacks account for a great deal of the costs associated with being compromised. No matter what the motivation is for the user to exfiltrate information out of the network, it happens. Whether it is done on purpose, or on accident, the impact may still be the same. It is important that the IT Security Professional to look at all threats to the business and take the needed steps to help prevent them. Note: The actions that I describe here are based on observation and coordinating efforts with others within the organization. Please contact your legal counsel to determine the right course of action and to protect the company from any legal ramifications. In addition, establishing a policy with how these types of situations arise may help to negate any sort of legal liability to your business as well.
0 Comments
securing healthcare data If you have not been to a healthcare provider in the last few years, you are missing out on the amazing transformation. The transformation will effect all of us and the quality of the lives that we lead, both now and in the future. Whether it is the use of technology in how your healthcare is delivered (telemedicine, or smart monitoring apps) or monitored. The impact has so far been enormous. With the interaction between the doctor and the patient becoming more interactive. The development of more healthcare provider apps only helps to facilitate this process. Which allows for the ability to provide enhanced healthcare services to their patients. Advancing Medical Technology While most of us would be cautious when it comes to adopting new technology, I am looking forward to the transformations that it is bringing. New technologies are being developed every day that allow new interaction with the healthcare provider and those they care for. Whether it is how the data is analyzed or developing new ways to deliver that analysis, the information age has finally come to healthcare. Technology Challenges While there are continuing advances in healthcare, there are also new challenges that companies will have to weigh as they continue to increase the amount of data they collect on an individual patient. Securing the data has now become the focus of the healthcare industry service providers. Whether it is in the cloud, or on premises, your data needs to be protected. With new ways to collect data, the data streams may be both, diverse and many. Collecting and storing this data will be an ever-increasing issue for hospitals and clinics as they become ever more data driven service providers. While analyzing data will provide enhanced or more focused services and treatment. What happens to that data after it has been used is still one area that providers continue to struggle with. Data Overload While data is crucial to the healthcare revolution that is going on these days, it is also one of the reasons that providers can do more with it. Whether it is sensitive information, or data about the condition of the patient, healthcare providers need to secure it. Some areas of focus for the IT Security Professional should be:
Increased Capabilities
With all the additional data points that are being created, it goes without saying that the capabilities of analyzing this information is increased. The use of supercomputers and large data sets will allow healthcare providers to look at the minutest details in order to determine patterns. The new analytics can in fact save lives by providing the healthcare worker with insight into areas that may not have been connected before. Whether it is providing a centralized location for all of the data on a hospital floor. Setting off alarms when certain conditions are met, can be one use of this constant monitoring that happens. The new analytics can improve your health in ways that were only a dream a few years ago. Connecting the dots when looking at data helps to increase the efficiency of the healthcare system and provide needed resources to those that are going to benefit the most from them. Star Trek Technology When I look at the hospital, I’m hoping one day to walk into an exam room and it look like the sickbay like on Star Trek: Voyager or Star Trek: Deep Space Nine. While sadly those dreams are a few years out yet. The ideas behind them are developing day by day. With wireless technology or the interconnected networks that make up the hospital infrastructure, it is important that patient data is protected from anyone not authorized to access it. While the tricorder doesn’t currently exist, the advances that we have made in the use of technology have made such a device a matter time, instead of an “if”. These devices will provide their own challenges as we continue to determine what information is needed and what is merely background noise. Some of this data will be essential to the new technology, and some will not, but what do you do with all those data-points that are not used? Databases Galore When a new technology is developed, it is usually with some essential benefits that it brings or it may fill a gap between two divergent technologies. Enabling the new technologies may require the creation of databases and the analysis of hundred and millions of data points. While these may be insignificant in and of themselves, they can in turn provide detailed information that could lead to new insight into potential threats to patients receiving treatment, they can also help to determine a cure to a disease that may not have been noticed before. The use of large databases such as Watson by IBM (www.IBM.com ) can lead to new ways of thinking about data. After all, we are continuing to create data points with our everyday activities and these when compared to others may show a correlation between unrelated events. These data points would be stored in these large databases and can be accessed for the wealth of information they contain. But how do we secure it? Increasing Security Needs All of these can cause an IT Security Professional to be restless at night, or have nightmares about having their data breached. The increased amounts of data that is being generated by healthcare technologies needs to be protected. Whether it is perimeter security, or securing the data at rest in your data center, you are now the custodian of these huge amounts of data. Security comes in many forms, but creating a robust program continues to be what it needed to deal with the issues of securing this data, both at rest and in transit. Monitoring information can be difficult to isolate in that it may be used in an immediate situation, such as; heart monitoring equipment or blood pressure cuff readings. These specific issues may cause the IT Security Professional angst and heartache, but it can be overcome. Summary Technology is continuing to advance in ways that we have never thought of before, and the advancement is being driven by data and the collection and analysis of that data. Whether it is on your wrist or connected monitors on your chest, data comes in many forms. It is the job of the IT Security Professional to help the company to protect that data. We have to provide guidance to the business in how they can be in compliance with current federal, state, or international regulations in regards to protecting patient information. The healthcare industry is at the forefront of making technological advances, and with new ways to capture data and providing detailed actionable information about it. These advances are going to continue to be developed over the coming years. These developments will continue to drive the IT Security Professional to being more of a data custodian than anything else. While data is needed in order to provide robust analytics, it is what happens to that data after the patient leaves the hospital or clinic that we have to worry about. The Results are In While most of the focus of pen testing rests on getting the test setup and configured in a way that will provide your business the most bang for its buck. It is important to remember that the results are what will help you drive IT Security within your organization. The data that is provided will be invaluable to helping you harden your network for the next round of testing. Raw Data Once the testing is completed, the raw data that you get from the testing team will help to determine your next steps. This data may need to be parsed or massaged into a form that may be consumable for members of the management team. This data will have information that may be useful to you, but your executive team may get lost in the nuances of what type of vulnerabilities were found on your web server. Priorities Determining the priorities and the remediation effort that you will give to each of the various levels will be the top issue once you get the data back. While there are various ways in which to separate this information, validating the information will be one of your critical tasks. Some common ways of sorting these vulnerabilities are:
Counting Down Once it has been determined the value that will be given to the vulnerabilities that were found during your penetration testing. The important work will begin, and that will be the remediation of those vulnerabilities in a timely manner. How long should you give to your remediation efforts? This is a question that all IT Security Professionals will ask themselves as they look at the amount of work that is now set before them. The time should be limited and doable based off the available resources you have. Also, depending on the number of vulnerabilities that were found, you may want to have a little time to make sure that you will be able to accomplish all the updates and patching before the next test is to take place. Whatever you do, it should be done with a sense of urgency since now that you know about these possible threats, (you aren’t going to sleep for a while, if ever again…) and the potential impact they may have on your company. This will be one area in which you will have to make sure that you have buy-in from your management team and they understand the potential threat to the business. Testing Frequency
When conducting pen-testing attacks against your network, you want to make sure that you are getting the most bang for your buck, (pun intended here) in that you get the most valuable information in which you can take action with. Whether you are following PCI DSS or HIPPA, or even GLBA. You will have to test on a regular basis and have a clean test (meaning that there were no HUGE issues found) which means you met the minimum standards. These requirements range from just once a year, to once a quarter for some regulations. A good rule of thumb is to allow the remediation efforts to have been completed and your Patch Management and Change Management Programs to kick into full gear again after the testing has been completed. This will be the most realistic for the additional data points that you will get from another test conducted in a short amount of time after the first. In addition, the pen-testing firm may offer follow-on testing as well, which will target those key areas where you may have had trouble or may have been a high-risk area. Summary Whatever choices you make concerning pen-testing; it is an important tool in the toolbox of IT Security Professionals. The services of Ethical Hackers can be an invaluable service to companies as we live in a world full of ever-increasing threats. Whether you are conducting testing on a yearly basis or every quarter, the data that you will find in the testing report will allow you to harden your network against those threats. |
IT Security ProSecuring the future one byte at a time! Mr. Barlow is here, staying ahead of the curve in Information Security Leadership. Ready to help your company stay safe and secure. Categories
All
Archives
January 2023
|





 RSS Feed
RSS Feed