| THE IT SECURITY PROFESSIONAL |
Barlowtek
The It security Pro
Helping Organizations Understand IT Security
&
Best Practices
Preventing an AttackPoint-of-Sale solutions are being utilized in ever-increasing numbers. This even more so during this holiday season as more and more companies see the benefit to using these devices. Whether it is in the retail environment or in the hospitality industry, Mobile POS solutions are making their way into different industry segments such as retail, and hospitality. This is especially true of the hospitality industry as more and more organizations embrace the ability to have mobile solutions for their customers to run their credit card transaction through. Here are a few of the ways that may be taken to secure your POS systems from a potential attack:
Development of secured firmware should be the focus of POS solution providers. Designing processes and systems that check the firmware for any deviation off what was previously installed or downloaded is one way that businesses will be able to secure the application that actually runs on the mobile device. Additional hardware checks should also be made that prevents any change to the interaction between the hardware and the firmware that is installed on it. This prevents the manipulation of the software and changing the parameters of coding process. These are areas that are discussed with any POS solution provider and should be an integral as part of your security posture. The software that is deployed on the hardware solution should also support the capabilities and reinforce the overall security processes that are utilized. Hardware and firmware should work in conjunction to secure the POS device from potential compromise (either of the hardware or of alteration to the firmware itself). This layered security approach provides a robust response to potential threats. EMV No Longer Cuts It The slow rate of adoption of the EMV smart card payment standard (A.K.A. chip and PIN) in the U.S. is one of the primary drivers for the repeated attacks on U.S. retailers. EMV requires a significant investment for companies to implement, and will not improve security for card-not-present transactions such as online or mobile purchases. As a result, chip and PIN alone will not be enough to protect retailers or merchants in the future. Businesses should focus on developing technologies and processes (such as end-to-end encryption and two-factor authentication) that would enable secure payment methods and protect consumers from evolving threats now, and in the future. Additional control technologies and systems will need to be adopted on a larger scale in order to protect consumers who use POS solutions. Multi-factor Authentication (MFA) has proven to be a viable addition to controls that are currently in place. Having additional steps put into place prior to processing a payments allows for further verification of user. In addition, the combination of biometrics and MFA has shown great promise, but providers are slow to adopt due to the cost of the implementation of the process and hardware that is needed to support it. Mobile Solution Adoption
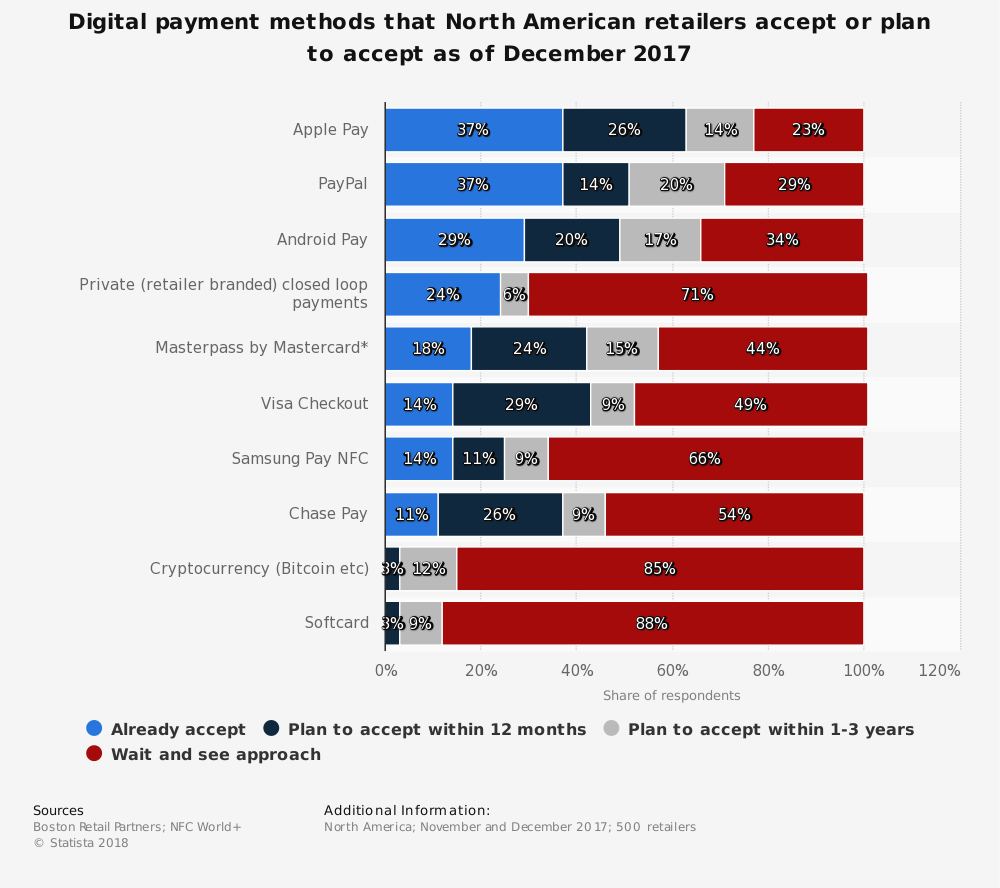
While mobile solutions have the promise of solving most of the security issues that have been outlined in this blog. The actual adoption and use of those technologies has not panned out as expected. With the use of Apple Pay or Samsung Pay, most retailers and merchants either have adopted for a specialized service or support that method that is used by the hardware device that they have adopted as their POS solution. While a large number of solution providers use Near-Field-Communications (NFC) capabilities of the customer’s mobile device in order to provide the interaction for the processing of credit card data, not all mobile devices support this feature. This leaves the contact-less adoption rate lacking. In order to get more merchants to adopt this technology it has to provide more security than is provided currently by other solutions that just require the EMV chip. Summary With the growing number of breaches, happening through the compromise of a POS solution it is imperative that solution providers take the necessary steps to protect the end consumer. Customers are demanding more security from the organizations that process their credit card payments. Whether it is the security on the back-end of the process or the interaction with the device itself, the credit card payments industry has to do more to protect sensitive data. Regulatory requirements are being implemented and mandated by governmental agencies at an ever-increasing rate. While these laws provide the drive for the adoption of these controls. The slow adoption rate by the end consumer has led to a hole in protections that attackers are taking advantage of to breach accounts. Businesses will either demand stronger controls their POS solution providers, or face additional penalties for not implementing the controls and greater overall legal liability. The solution is simple, demand more security and implement it across the board with all POS solutions. That is easier said than done.
0 Comments
Crypto-Currency Payments Using POSWhile there are many articles expounding on the security of using blockchain technologies for various reasons, it seems very impractical to use it as part of a POS solution. Blockchain can have many moving parts that need to function correctly in order to make things run smoothly. The main use of this technology has been the development of crypto-currencies such as BitCoin. But, are customers willing to use their crypto-currency accounts to pay for their meals, or event services? Difficult Integration While blockchain technology is quickly developing into a methodology that helps to secure monetary transactions. POS Solutions will have a difficult time integrating it into the firmware that they use to power their devices. Being able to integrate into the larger payment and online infrastructure that houses the crypto-currencies can be difficult to secure, not to mention to achieve PCI compliance as well. Currency Volatility The market on the crypto-currency market has been very volatile recently and currency stability is something that businesses will want to have in place when they receive payments from a consumer. If the crypto-currency is worth less today than when the payment was accepted. Who will pay the difference? Individuals that invest in crypto-currencies know that the market is volatile and they are in it for the long haul as they can be rewarded for their patience, or they can get soaked with a loss. But that is the nature of the market, and they accept that as part of the risk. Lack of Adoption Crypto-currency is more of an enigma for most people. Not very many people are into the market for them and they are not widely adopted as a way to pay for everyday items. Uses for BitCoin have been for illicit transactions on the dark web. This has also lead to the introduction of crypto-currency as already having a stigma attached to it already. In order for the use of crypto-currency to take off and be useful as another way to pay for a service or manufactured goods, it needs to be widely adopted. The current market of these currencies does not hit that mark. Enabling customers to pay with the currency might be a good thing for the service provider, but the return on the investment on a system that can allow that to happen will be very minute. As mentioned before, the volatility of the crypto-currency market make it a losing deal all the way around. Payment Method Integration While the use of crypto-currency remains a buzzword today, other methods have been around longer that are still not being adopted as they were originally touted to do so. In addition, some of the technologies that are currently available like Near-Field-Communications (NFC) have not been fully enabled or utilized by merchants, or POS solution providers. This leads to the question; why another technology? Currently several technologies can overlay with the current payment card processing that solution providers follow. These technologies enable the physical card to be more secure, or help to prevent unauthorized use and disclosure of the primary account number (PAN) and other track data. Any one of these would help to prevent attackers from stealing this data. Nevertheless, they have not caught on with the public as a means to pay for their goods or services. Virtual Card vs. Crypto
There is a growing interest in the use of virtual soft-card technologies that will enable the consumer to pay for a product or service without having to have a physical card. The virtual card will generate a unique credit card number that will be specific for that transaction, and then disabled after that use. This secures the number against any further transactions or usage. Using a virtual card uses current technologies and is processed in a similar fashion as a card-not-present transaction. Crypto-currency is volatile and the amount it is worth may change during the processing of the payment to the merchants bank. In addition, integration into with blockchain technologies over the web in order to record the transaction may not be secured according to PCI requirements leaving the liability of the transaction on the merchant. Crypto-currency integration will require additional infrastructure and processes in order to allow it to be adopted as a means of payment. Virtual cards utilize current infrastructure and processes while also providing no hard payment device that could possibly be compromised. Technology Adoption & Implementation As the payment card industry continues to deal with how to deal with regulatory requirements and making the consumer’s credit card transaction more secure. Technology is advancing that can address these issues. Some of them make a great deal of sense and can be readily implemented. While others are more difficult and will require a great deal of infrastructure improvement in order to adopt the solution. The technology has to help secure the process or help to reduce the threat of a potential compromise. The latter of which has been the driving force for the adoption of current technologies that have been mandated by PCI for the payment card industry. This does not mean that there are new and emerging technologies that shouldn’t be looked at for solving this problem. On the contrary, all options should be on the table as solution providers find new ways to support the merchant, but also helping to secure the customers transactions. Summary It is important to remember that BitCoin has only been around for about ten years now and the technology that has powered it continues to grow and develop. As people get more used to the use of crypto-currencies and we see, electronic wallets become commonplace. The use and development of POS solutions that integrate with crypto-currencies will be limited. That is not to say that there will not be a large number of potential merchants that want to use them in the future. Nevertheless, with current technologies being what they are, it will be difficult to integrate the infrastructure that will be needed to support such a solution. In order to make the adoption of crypto-currency accepting POS solutions viable, the use of the currency needs to be more widespread and accepted. Even with current alternative payment methods being available, the public is not using them in the high numbers that you would want to see with a new technology. Without the customer base that would use a solution, the costs for the adoption of a solution that uses it would be too much, which would offset any sort of security protections that you would get from it. Reducing PCI Liabilities Securing Credit Card Transactions Restaurant chains and many retail organizations continue to be the targets of attackers who are trying to exfiltrate customer data out of the organizations network. While there are many ways that an attacker can accomplish this, the one that seems to be the most effective has been to compromise the physical hardware or software that collects the customer information. While the process for compromising a POS system is fairly easy for some, there are a few things that need to be in place for this to be effective, and for the attackers to get away with it. This uptick in breaches and attacks is one of the reasons that we have seen updated security regulations coming out of the banking institutions for the Payment Card Industry (PCI) (www.pcisecuritystandards.org) with an upgrade to their requirements to 3.2. Payment Security PCI has established guidelines that all businesses that accept payment cards must follow with regards to establishing and maintaining the ability to process those payments. Making sure that the transaction is secure and that the consumer data is not compromised is the name of the game here. Failure in this area and your name will be in the papers for the entire world to see (or these days, on the web). We have seen spectacular failures such as Target (www.target.com), Applebee’s (www.applebees.com), and Forever21 (www.forever21.com). While some of these breeches can be directly related to the vulnerabilities related to the hardware itself, others have been due to a compromise of the software that is used, or an infection of malware. Addressing these vulnerabilities by an organization is of the utmost importance and should be the focus of any solution provider. If these processes fail, it is the customer and the merchant that pays the price. Security In-depth When it comes to payment processing, having security in-depth is needed. What do I mean by that for a POS system? I mean that the hardware and software work together in making sure the payments are transmitted to the banking institution in an encrypted format that protects the customer’s data. Developing software that uses the hardware is similar to what Apple (www.apple.com) has done with their production of the iMac or MacBook. Creating proprietary software that helps support the security controls that are already available on the hardware can go a long way in securing the device from being tampered with (which is one of the areas that an attacker will try to compromise a system). Hardware design also helps. One Stop Vendor The key areas that a merchant can do to help reduce their risk and liability is by looking at various solutions that meet their needs. As a work-around, restaurant operators may opt to work with one company to meet all their needs. “When it comes to choosing a vendor, if we could get something through our POS provider we will do it because we know it will integrate well rather than having to find a loophole,” says Michael Jackson, director of logistics at Kerbey Lane CafÉ (www.kerbeylanecafe.com) in Austin, Texas. Jackson uses NCR’s (www.ncr.com) Aloha POS (www.alohancr.com) system, kitchen system, mobile POS, loyalty solution and more. This approach, however, can lead a restaurant to prioritize the benefits of a one-stop provider over hand-picking “best-of-breed” suppliers; that is, those with deep expertise in one area, such as loyalty or social commerce. (Mastroberte, 2014) The business must weigh the cost-benefit of choosing a provider that they can rely on for all of their services, or hobble together bits and pieces from different providers. While some larger restaurant chains are able to develop their own solutions, others are relying on dedicated organizations that specialize in creating and developing an all integrated solution (utilizing dedicated hardware and software). Reducing Risk & Liability Utilizing one solution provider for all of the services that a merchant might need (credit card processing and loyalty card payments) lowers the possibility that the solution components will not work well together. The solution provider who integrates both the software and the hardware (whether they produce them or not) has worked to develop the software to work effectively with the hardware that is used in their solution will function in a manner that protects the data being transmitted. When a merchant utilizes a certified solution provider for their processor for payments the provider takes on the liability with reduced merchant costs. With the market moving towards integrators and less on those that specialize in one or two components of the overall solution. The result will be a more secure POS system that is less vulnerabilities than in the past. (Don’t get me wrong, if somebody wants to get into your devices, they will find a way in). The new integrators are making that task more difficult. This is a step in the right direction in reducing the merchants risk and liability while also providing more secure solutions to choose from. Summary While the POS solution providers market continues to grow and more companies get into the game of providing solutions to their customers. The need for solution integrators is growing and will be pushed along by merchants and customers demanding their data be more secure. While there continues to be various devices on the market that meet these needs, not many have the security in-depth that I mentioned above. Merchants can choose to go it alone and except the full liability and risk, or they can choose an integrator that provides a whole solution. The latter being the way to help secure the customer’s payment card data and reducing overall PCI liability. References Mastroberte, T. (2014, August 6). POS Integration Becoming a "Must-Have". Retrieved from hospitalitytech.com: https://hospitalitytech.com/pos-integration-becoming-must-have Additional Links Forever21 https://www.forever21.com/protecting_our_customers/default.aspx Target https://krebsonsecurity.com/2015/09/inside-target-corp-days-after-2013-breach/ Applebee’s https://www.scmagazine.com/applebees-hit-with-pos-breach/article/749139/ |
IT Security ProSecuring the future one byte at a time! Mr. Barlow is here, staying ahead of the curve in Information Security Leadership. Ready to help your company stay safe and secure. Categories
All
Archives
January 2023
|




 RSS Feed
RSS Feed