| THE IT SECURITY PROFESSIONAL |
Barlowtek
The It security Pro
Helping Organizations Understand IT Security
&
Best Practices
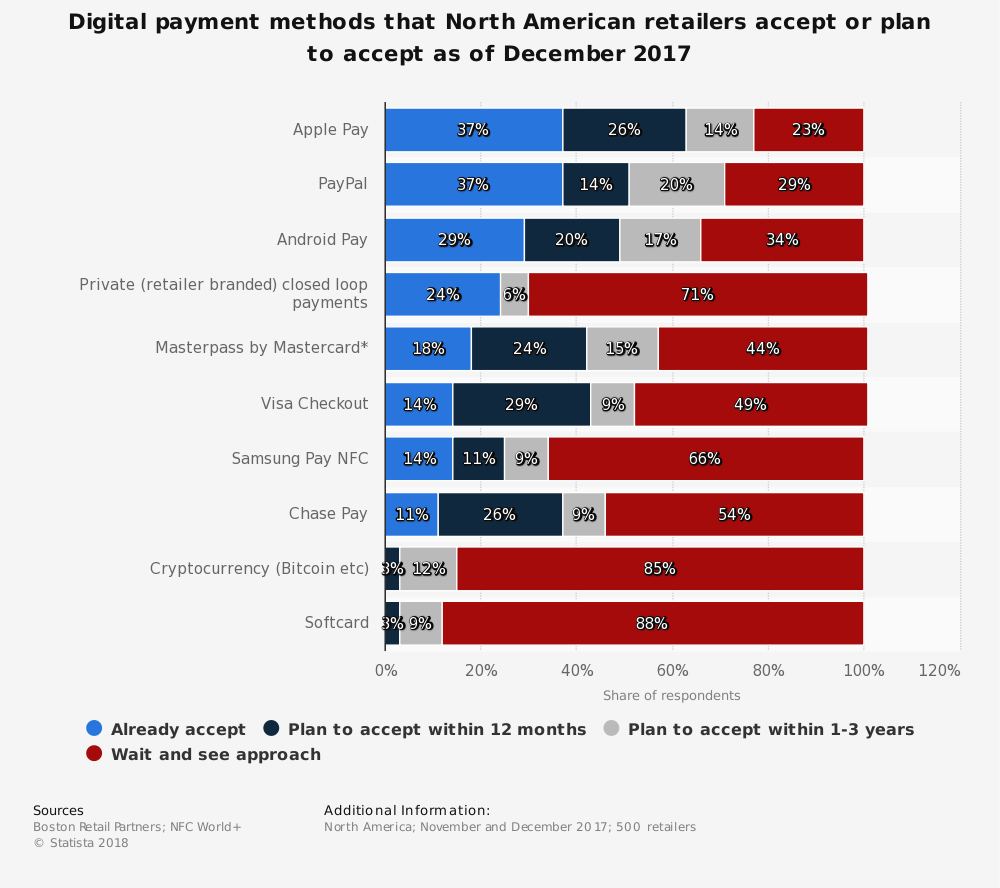
Crypto-Currency Payments Using POSWhile there are many articles expounding on the security of using blockchain technologies for various reasons, it seems very impractical to use it as part of a POS solution. Blockchain can have many moving parts that need to function correctly in order to make things run smoothly. The main use of this technology has been the development of crypto-currencies such as BitCoin. But, are customers willing to use their crypto-currency accounts to pay for their meals, or event services? Difficult Integration While blockchain technology is quickly developing into a methodology that helps to secure monetary transactions. POS Solutions will have a difficult time integrating it into the firmware that they use to power their devices. Being able to integrate into the larger payment and online infrastructure that houses the crypto-currencies can be difficult to secure, not to mention to achieve PCI compliance as well. Currency Volatility The market on the crypto-currency market has been very volatile recently and currency stability is something that businesses will want to have in place when they receive payments from a consumer. If the crypto-currency is worth less today than when the payment was accepted. Who will pay the difference? Individuals that invest in crypto-currencies know that the market is volatile and they are in it for the long haul as they can be rewarded for their patience, or they can get soaked with a loss. But that is the nature of the market, and they accept that as part of the risk. Lack of Adoption Crypto-currency is more of an enigma for most people. Not very many people are into the market for them and they are not widely adopted as a way to pay for everyday items. Uses for BitCoin have been for illicit transactions on the dark web. This has also lead to the introduction of crypto-currency as already having a stigma attached to it already. In order for the use of crypto-currency to take off and be useful as another way to pay for a service or manufactured goods, it needs to be widely adopted. The current market of these currencies does not hit that mark. Enabling customers to pay with the currency might be a good thing for the service provider, but the return on the investment on a system that can allow that to happen will be very minute. As mentioned before, the volatility of the crypto-currency market make it a losing deal all the way around. Payment Method Integration While the use of crypto-currency remains a buzzword today, other methods have been around longer that are still not being adopted as they were originally touted to do so. In addition, some of the technologies that are currently available like Near-Field-Communications (NFC) have not been fully enabled or utilized by merchants, or POS solution providers. This leads to the question; why another technology? Currently several technologies can overlay with the current payment card processing that solution providers follow. These technologies enable the physical card to be more secure, or help to prevent unauthorized use and disclosure of the primary account number (PAN) and other track data. Any one of these would help to prevent attackers from stealing this data. Nevertheless, they have not caught on with the public as a means to pay for their goods or services. Virtual Card vs. Crypto
There is a growing interest in the use of virtual soft-card technologies that will enable the consumer to pay for a product or service without having to have a physical card. The virtual card will generate a unique credit card number that will be specific for that transaction, and then disabled after that use. This secures the number against any further transactions or usage. Using a virtual card uses current technologies and is processed in a similar fashion as a card-not-present transaction. Crypto-currency is volatile and the amount it is worth may change during the processing of the payment to the merchants bank. In addition, integration into with blockchain technologies over the web in order to record the transaction may not be secured according to PCI requirements leaving the liability of the transaction on the merchant. Crypto-currency integration will require additional infrastructure and processes in order to allow it to be adopted as a means of payment. Virtual cards utilize current infrastructure and processes while also providing no hard payment device that could possibly be compromised. Technology Adoption & Implementation As the payment card industry continues to deal with how to deal with regulatory requirements and making the consumer’s credit card transaction more secure. Technology is advancing that can address these issues. Some of them make a great deal of sense and can be readily implemented. While others are more difficult and will require a great deal of infrastructure improvement in order to adopt the solution. The technology has to help secure the process or help to reduce the threat of a potential compromise. The latter of which has been the driving force for the adoption of current technologies that have been mandated by PCI for the payment card industry. This does not mean that there are new and emerging technologies that shouldn’t be looked at for solving this problem. On the contrary, all options should be on the table as solution providers find new ways to support the merchant, but also helping to secure the customers transactions. Summary It is important to remember that BitCoin has only been around for about ten years now and the technology that has powered it continues to grow and develop. As people get more used to the use of crypto-currencies and we see, electronic wallets become commonplace. The use and development of POS solutions that integrate with crypto-currencies will be limited. That is not to say that there will not be a large number of potential merchants that want to use them in the future. Nevertheless, with current technologies being what they are, it will be difficult to integrate the infrastructure that will be needed to support such a solution. In order to make the adoption of crypto-currency accepting POS solutions viable, the use of the currency needs to be more widespread and accepted. Even with current alternative payment methods being available, the public is not using them in the high numbers that you would want to see with a new technology. Without the customer base that would use a solution, the costs for the adoption of a solution that uses it would be too much, which would offset any sort of security protections that you would get from it.
0 Comments
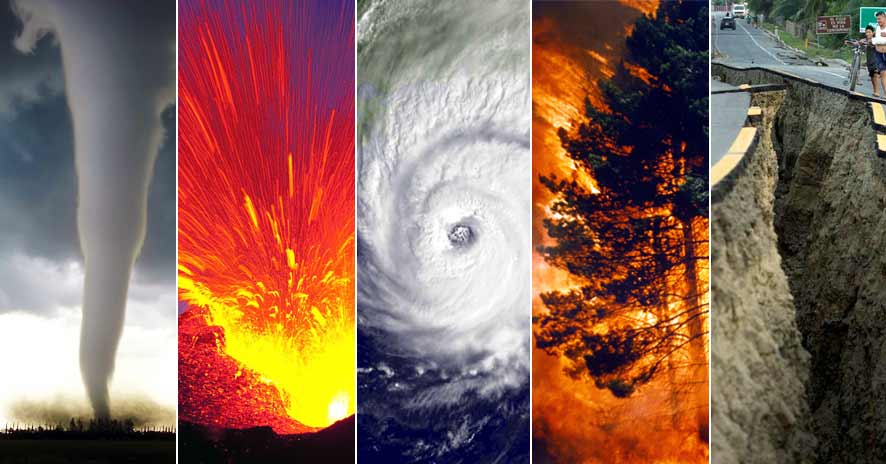
Making a PlanWhen it comes to disasters, you never know what type will hit your organization. How do you know what to prepare for? There are so many things that could go wrong, and planning for all of them will definitely impact your bottom line. Planning for the most likely event or one that would have the most impact on your business might be the way to go. Nevertheless, regardless of what you decide to prepare for, you need to have a plan. Plan Development Develop a plan outline that addresses all of the various areas that could be impacted during a disaster. (A disaster for this blog is anything that could potentially impact your organization or hinder its normal operational tempo). Below are a few of the areas that should be included in your Disaster Plan (DP):
Areas of Focus For most businesses, you will want to get up and running as soon as possible and it is for this reason that you will want to be a thorough as you can with your planning process. There will also be additional documents/evaluations that will be included in the planning process for the DP, which are:
Bringing it Together When developing the DP, it is important to have finished the supporting documents and conducted the various evaluations. This will take time, as you will want to talk with all of the stakeholders in your organization and gather their input. (The plan should not be prepared in isolation from the rest of the company, but be inclusive). Including the findings of the supporting documents and findings will help to flesh out the DP as you specifically address those areas. Using diagrams and flow charts will also be an important part of the plan. These will help to illustrate the plan and provide additional detail that may not be in other areas of your document. Creating process flows and decision trees will be an important part of the development process as these may change depending on the scope of the incident. Including additional content will also help to explain specific requirements of the DP, as there may be a need to include lists of employees, vendors, and other support personnel who will need to be contacted in case of an incident. Communicating the Plan You have gathered all of the stakeholders in your organization and they have helped bring the plan together. After the plan has been signed off, and adopted by your organization, you will need to communicate the plan to the rest of the business. How do you do this? There are several effective ways, but making sure that all of the people that you listed (assigned duties to) know what they are responsible for and what they are specifically required to do for the plan. Depending on what your specific organization handles employee communication, the plan could be communicated through an email, or a classroom training session. Both of these can be effective as they provide a way to pass along the information that the employee’s will need to know. When a disaster hits your company, you don’t want people to wonder what they are supposed to be doing during the event. You are only as prepared as your last test. Testing the Plan
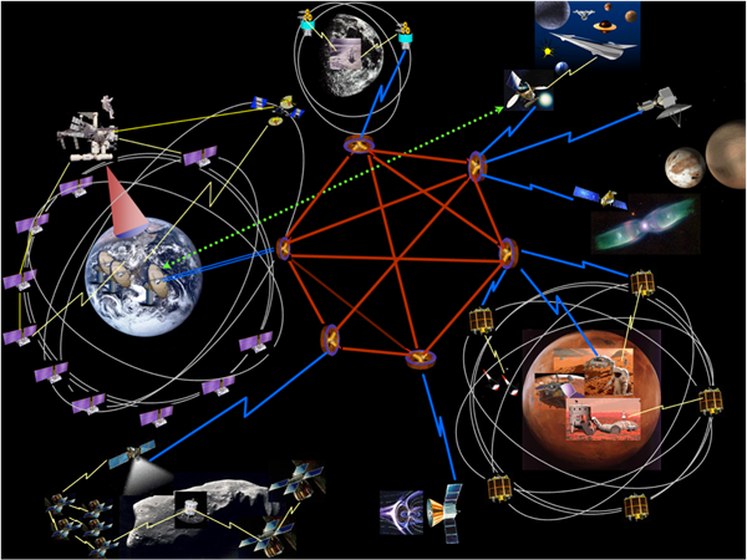
Probably the most important part of the plan is the testing of the DP. You should be testing your plan at least on an annual basis to make sure that it is still valid. In addition, updating your plan throughout the year is not a bad idea either, as your environment may change with additions or upgrades to current technologies. The plan should be a living document, in that it reflects the current situation of your organization. If it does not, make sure that you address it as soon as you are able to do so. At a minimum, a tabletop test of your plan should be performed with all of the stakeholders and those with responsibilities outlined in the DP itself. Testing should be documented and the findings addressed if there are any. This will provide areas that will need to be addressed in a timely manner. For most certifications, having a DP is a must and the organization needs to show documentation that they are testing it on an annual basis, so this will help with any of those compliance requirements that you might face. Summary While there is, a lot that will go into a DP, in the end it is worth all of the effort when you see the plan in action. Developing the plan when you are not stressed with an incident allows you to think through the situation in a calm and collected manner. Developing a DP is one of the most important items that an IT Security Pro can do to help their organization. Whether it is making changes to the plan, or finding a solution that will meet the needs of the business. It is also important to make sure all areas of the business are addressed and that the plan takes into consideration contractual and regulatory requirements as well as specific needs of the company. Securing Interplanetary NetworksIf you have been watching the news recently, you have seen that there is a growing interest in space exploration and colonizing places such as the Moon or perhaps even Mars. These efforts are continuing to bring up questions about how we are going to deal with IT Security in an age when the use of networks and infrastructure are critical to human survival on these alien worlds. How do we deal with these issues? These are just some of the questions that we will have to answer in the coming years of space exploration. Space Networks We will need to have secure and reliable computer networks that will integrate with the terrestrial network that we have here on Earth. These space networks need to be able to use various methods to transmit data. Whether it is to plug into the satellite network, or the use of an on-planet integrated network like on Mars or the Moon. The international community will have to adopt these protocols and standards that address inherent issues associated with communications from space. We will want to get that data to others that may most likely be out of the same network. This means that the data will have to be transmitted out of network to a designated location. These networks or network segments will just need to work, and work reliably all the time. The interoperability of these networks will ensure that the communications and data that are sent over them will function, even if they are transmitted back here on Earth. Delayed Transmission When it comes to outer space, distance is one of the biggest hurdles that will need to overcome. It takes time to get from one point to another and that time adds up. The further you are away from the Earth, the longer it will take for those signals or transmissions to make the trip to the Internet. While the Interplanetary Internet is still in its infancy, we need to make sure that IT Security issues are addressed right from the outset. There will be times that the transmission may be delayed due to where it is being sent from, and so that data will be vulnerable to potential attack and compromise. Sending back valuable information to the Earth about specific details on resources available could potentially be profitable to the right people. This is even more reason why we need to make the security of the Interplanetary Internet even more of a priority. Best Practices for Space Just like here on Earth, there will be some best practices that we can employ when looking at the Interplanetary Internet. Some of them are:
Life or Death Networking When it comes to working and soon to be living off planet. It is important that the computer network is working and functional for those that are dependent on it for their survival. Whether it is monitoring the habitat or the space weather, those individuals that are dependent on it will want to make sure that the information is accurate and correct. If there is a compromise of the habitat or an air lock, people may die because of it. Space travel and planetary colonization is dependent on things that work and that have redundancies built in due to the potential for things to go wrong. This is especially true when it comes to developing the colony on Mars. It will take at least seven months for help to arrive, and by then things might have already gone wrong. Pushing out to the planets and the stars will stretch our ability to maintain communications, but it is now that we need to work on making them secure. Summary It is an exciting time to live in the world that is on the brink of a world-changing event such as creating a colony on the Moon or even Mars. What was once science fiction will become science fact as we start to fill in the gaps in our textbooks. Humanity has had so many questions about how we develop life beyond our planet, now we will actually start working on those answers. Moreover, computers and computer networks will play a major role in the ability of those brave space pioneers to accomplish their missions. We must do everything in our power to secure them and make sure that they can depend on them to work when they need them to. Article Update: 03/22/2019 On March 2, 2019 at 2:49 a.m. ET Elon Musk's SpaceX crew Dragon spaceship docked with the International Space Station (ISS) in an unmanned automated mission to certify the spacecraft. This was a momentous occasion for NASA as they will be certifying the first private space company to ferry astronauts to space by not having to rely on the Russian Space Agency to get American astronauts into space. The Crew Dragon Spaceship was not the only thing launched to the ISS, a dummy was also on-board as well. The next step is to have a human crew on-board the Crew Dragon Spaceship, which as of the date of this post has not been determined yet. With all of the exciting things going on in space, things are looking up for continued exploration of space on a timeline that is both aggressive and achievable.
Technology is playing an important role in all of this progress in space. Networks and communications are becoming an integral part of moving our exploration out into space, but not just above the Earth, but also on the Moon and Mars too. How we are going to communicate and network these distant locals will be important as we start to develop both the means and the spacecraft to go there. It will be important to work with all of the various countries, and businesses to establish international standards on how networks will be setup and configured. Competition in Space Its not just private companies that are going to space either, it is countries like Israel, China, and India that have made the jump into space exploration. How are all these companies and countries gonna talk to one another? With rivalries here on Terrra Firma ratcheting up, we can only imagine what it will be like in space. Will each country put up their own infrastructure and nobody else will be able to use it? These are questions that need to be asked and worked out before we run into these issues. IT Security is also playing an important role as well. It is helping to establish various protocols and guidelines for organizations to follow. When the international community starts to piece together all of these various pieces, they will be able to have a robust infrastructure in which to rely on. Establishing space relay stations for communications into deep space will allow the time that data normally takes from one location to another in space to be cut down, and also boosting the signal strength at the same time. This will be important to work on together, not as just one nation, but also as a global community. Securing Your ResourcesWhen it comes to the use of cloud technologies for providing services for a business or organization, the main benefit that is quoted is the overall cost savings. Lower bills and a better quality of service offered to the end consumer or user. While these are great for the initial introduction to the cloud, securing that new expanded infrastructure is now the focus for most IT Security departments. How will they do it? Who has the responsibility to do it, and who will take the blame if there is a breach of that security? These are all questions that must be answered prior to any business adopting the hybrid or straight cloud solution for their enterprise. IT Security should be the focus for any organization that is thinking of putting their assets and resources into an infrastructure that they don’t have full control over. Most cloud service providers will have enhanced security controls; they also still have weaknesses that will need to be overcome if you are planning to secure your infrastructure. Castle Model In ancient times (1990’s to be more precise) the main focus for IT Security was that we had a castle and that everything on the outside of our firewall (“castle wall”) was to be considered hostile and that everything on the inside was friendly and that we needed to make sure that the “bad guys” stayed out. This was good for a while and it still permeates the IT Security industry today with the focus on building the best firewall and detecting the enemy’s at the gate. As the technology has advanced, we have found ourselves looking at different models but still the same question. “How do we protect our end users and our networks from the bad guys?” Then came the cloud revolution in the 2010’s, and a whole shift came in the way that services and infrastructure were to be delivered to the end user or customer. The cloud offerings really came into their own as businesses of all shapes and sizes were moving their assets and resources to the could in order to take advantage of the new paradigm; cheaper, faster, better. Fast-forward It has now been about 10 years since that shift in infrastructure as we continue to see organizations take advantage of the savings that is available to have services provided in the could vs. on premises. Nevertheless, security remains an area that companies have trouble focusing on due to some of the complexities in the environment from which they work in. Who is responsible for a breach of infrastructure when the service provider is attacked? If I have control, does that mean that I am responsible? Benefits of the Cloud An organization will get several benefits when they move resources to the cloud or use some of the various services that are offered by vendors that rely on the cloud to provide it. Some of these are:
Securing the Cloud
When it comes to cloud security, it is important to remember that access to the cloud environment poses the biggest risk to any organization. Not knowing or having lax controls can allow for gaps within your IT Security Policy enabling potential threats to compromise the network. The following areas should be in focus for securing access:
Service Provider Security The benefit of having assets in the cloud is that the service provider will usually have more robust security processes in place than what you would be able to leverage. This ability lends itself to the development of a partnership between your company and the provider. When it comes to being able to work a security problem, it will be important to have professionals that are well versed in the technology to help out. This is what you get with a service provider that is looking to enhance your security measures. Monitoring Everything When looking at using a cloud solution provider (CSP) for your organization. It is important to remember that you are going to be monitoring everything within that environment. This is usually done via a GUI or some sort of online portal. It is important to take a look at these when you are looking at a provider. You will want to monitor the following:
Summary While the cloud is, continuing to grow and new services and resources are being added all the time. It is important to remember that IT Security remains the main factor for the slow adoption of the cloud services. With service providers, looking to build a better and more robust security posture for their clients. It is important to discuss concerns and specific requirements that your organization may have. This is where the partnership between your business and the CSP is built, which in turn, helps the IT Security Pro who has to maintain your cloud environment. Customers Unique DataWhen it comes to using POS systems, security is the name of the game. Providing ways in which to secure customer’s information in a way that uses more advanced technologies than what is currently available for the public today. The use of biometrics is a growing area, which is seeing more traffic in the payment card and hospitality industries. The use of biometrics in the transportation security by the airlines is also the growing. Customers are getting used to their biometrics being used. This has led to them being more comfortable with their usage, but especially if they know, it will help to secure their information. The ease of adoption of this technology will help to continue to grow the industries that are adopting it. This is especially true to for the hospitality industry. Limited Input When looking at the size and complexity of POS solutions, you will notice that size matters. In this particular instance, it means that the devices are small and compact. Which means they don’t have a lot of room to have additional input areas on the device itself. Whether the POS device uses thumb scanning technology or an iris scan, it is going to take additional resources that these systems currently are very limited on, at present. Solution providers will need to find a way to collect the required data and store the information in a manner consistent with current regulations. This may mean the addition of external input devices such as a camera or touch pad in order to collect the needed fingerprint data points. While the use of biometrics may be for various reasons, such as; employee access control, and fraud prevention. The focus will be to add this additional feature for use by the public for an additional security control in preventing fraudulent use of credit cards. Cryptographic Controls for Biometrics Cryptographic controls will need to be utilized for transmitting the sensitive data that will be collected on the customer. Customer’s personal information will also need to be stored and in a secured encrypted database where the information is highly available. The amount of data that biometrics creates can be enormous and complex to say the least. This sensitive information will also need to be provided to the POS solution software in order to validate the customer. This information will need to be accurate and transmitted to the device when presented with a customer paying for a service. All of the personal data that will be collected from the customer will need to have strict controls in place in order to make sure the information is not corrupted or altered. As with any technology, there are inherent issues with its use and adoption. This is especially true with the use of biometrics, due to issues with the data capture devices and how the information is read. These errors can affect the overall customer experience and may affect the overall adoption of the technology within the specific business. Driving Factors for Adoption Some of the driving factors for the adoption of biometrics within the payment card industry is the adoption of this technology by the issuing institution and their need to protect their customer data. Personal Identification Numbers (PIN) s are not able to provide the integrated security that both the industry and the customers are looking for. Adding biometrics also enhances the current security measures without adding an additional physical layer to the verification process such as using two-factor-authentication (2FA). The additional layer would require more from the customer while adding additional steps to the process. The industry is moving to a more streamlined experience with transactions taking less time to accomplish. Adding the additional control requirement defeats these efforts. Benefits of Biometrics
The benefits that biometrics bring to security cannot be understated. Their use has been a major improvement on the use of complex passwords or PINs. Biometrics provide a positive identity verification since the information provided and used is based on the individual and unique person for which access is granted. Additional benefits include:
Future Requirements While the payment card industry continues to struggle with fraud and data breaches, customers are demanding that more secure methods are adopted. The public wants their information to be secured and methods put in place that help to protect that data. In addition, international regulations are also pushing card issuers and processors to adopt more stringent verification methodologies that help to reduce the chances of fraud. Credit card data is one of the types of information that is readily convertible (the other being healthcare data) to making a profit for those that are able to sell the information. The adoption of the use of biometrics reduces the capabilities of those trying to commit fraud by making it impossible for them to use the information. Connecting biometrics to a credit card makes it almost impossible to make a charge without verifying the identity of the one making the transaction. More and more regulatory agencies are moving towards making the use of biometrics as a payment method mandatory due to the ability to reduce fraud. Summary We are all unique individuals, and that uniqueness is what makes the use of biometrics in the payment card industry one of the best ways to help to reduce fraud. The adoption of this technology will get stronger as more and more solution providers offer it for their solutions and customers are used to seeing it and using the technology. Customers are looking for better ways in which to secure their sensitive information, and biometrics is proving that it is up to the task. With so many ways in which an individual’s personal information can be obtained, the need for the adoption of biometrics in the payment card industry is only growing stronger. Those solution providers that are adopting it, or who are integrating it into their current solution will be ahead of the game as the market moves to more security, not less. |
IT Security ProSecuring the future one byte at a time! Mr. Barlow is here, staying ahead of the curve in Information Security Leadership. Ready to help your company stay safe and secure. Categories
All
Archives
January 2023
|







 RSS Feed
RSS Feed